The AI Kill Chain Explained: Two Frameworks Every Defender Needs
What a kill chain is, why AI needs its own, and how NVIDIA and MITRE ATLAS map attacks on AI systems stage by stage.
TL;DR: A kill chain maps every step an attacker takes, so defenders can break any one link and stop the whole thing. AI systems need their own because the attacks look nothing like traditional hacking. NVIDIA’s AI Kill Chain gives you the five stages. MITRE ATLAS gives you the technique catalog. Here’s how both work.
This is the public feed. Upgrade to see what doesn’t make it out.
0x00: What Is a Kill Chain and Why Does AI Need One?
A kill chain is a military concept borrowed by cybersecurity. It breaks an attack into sequential steps, from first recon to final damage. The original Cyber Kill Chain (Lockheed Martin, 2011) mapped seven stages of a network intrusion: find the target, build the weapon, deliver it, exploit a flaw, install malware, establish remote control, steal the data.
The power of the model is simple. If you break any one link, the whole chain fails. Defenders don’t need to stop everything. They need to stop one thing.
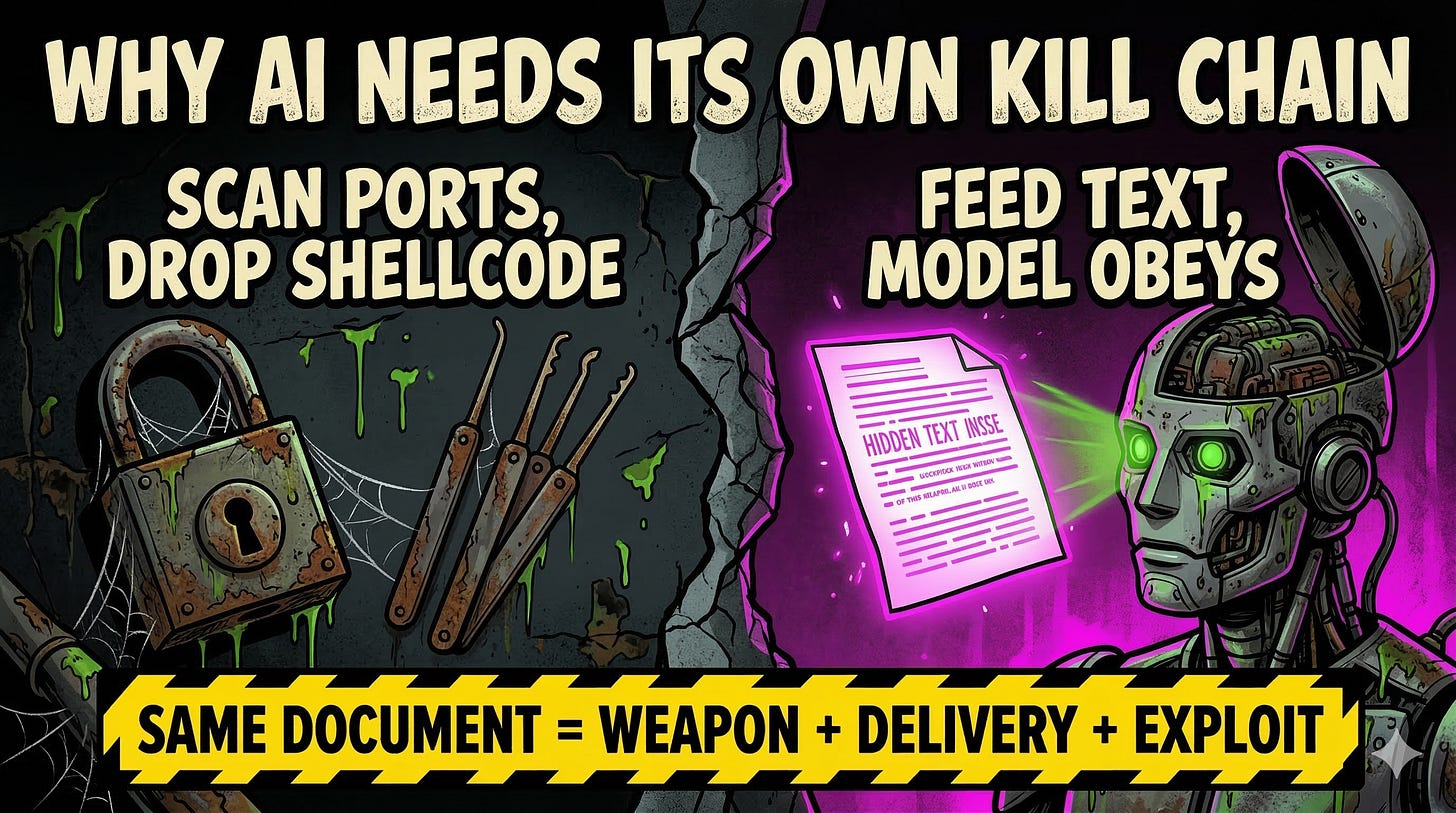
AI systems need their own kill chain because the attacks are structurally different. Nobody is scanning ports or dropping shellcode. An attacker feeds poisoned text into a model’s context window (the working memory the AI reads before responding), and the model does the rest. It reads the malicious input, treats it as trusted instructions, and starts executing tool calls on the attacker’s behalf. The weapon, the delivery mechanism, and the exploit can all be the same document.
Signal boost this before someone else gets owned.
0x01: How NVIDIA Maps AI Attacks in Five Stages
NVIDIA built the first widely adopted AI kill chain. Five stages: Recon → Poison → Hijack → Persist → Impact.
Recon is where the attacker maps the AI system. What model is running? What tools can it call? What data sources feed into it? This looks like probing the chatbot with weird inputs and watching what leaks out of error messages.
Poison is planting malicious content where the model will ingest it. That could be a document in a RAG database (a retrieval system that feeds external files to the model), a tampered tool description, or a tainted web page the agent browses.
Hijack is when the model processes the poison and starts following the attacker’s instructions instead of the user’s. The model becomes a proxy. It will read files, call APIs, and generate outputs the attacker controls.
Persist means embedding the compromise so it survives beyond one session. Poisoning the AI’s memory, saving tainted data to a database, corrupting a tool config. Next time any user triggers that context, the attack fires again.
Impact is the payoff. Data exfiltration. Unauthorized transactions. RCE through chained tool calls. The model didn’t get hacked in the traditional sense. It got convinced.
If someone poisoned your RAG database today, which stage would catch it? Comments are open.
0x02: How MITRE ATLAS Catalogs the Techniques
NVIDIA gives you the narrative. MITRE ATLAS gives you the encyclopedia.
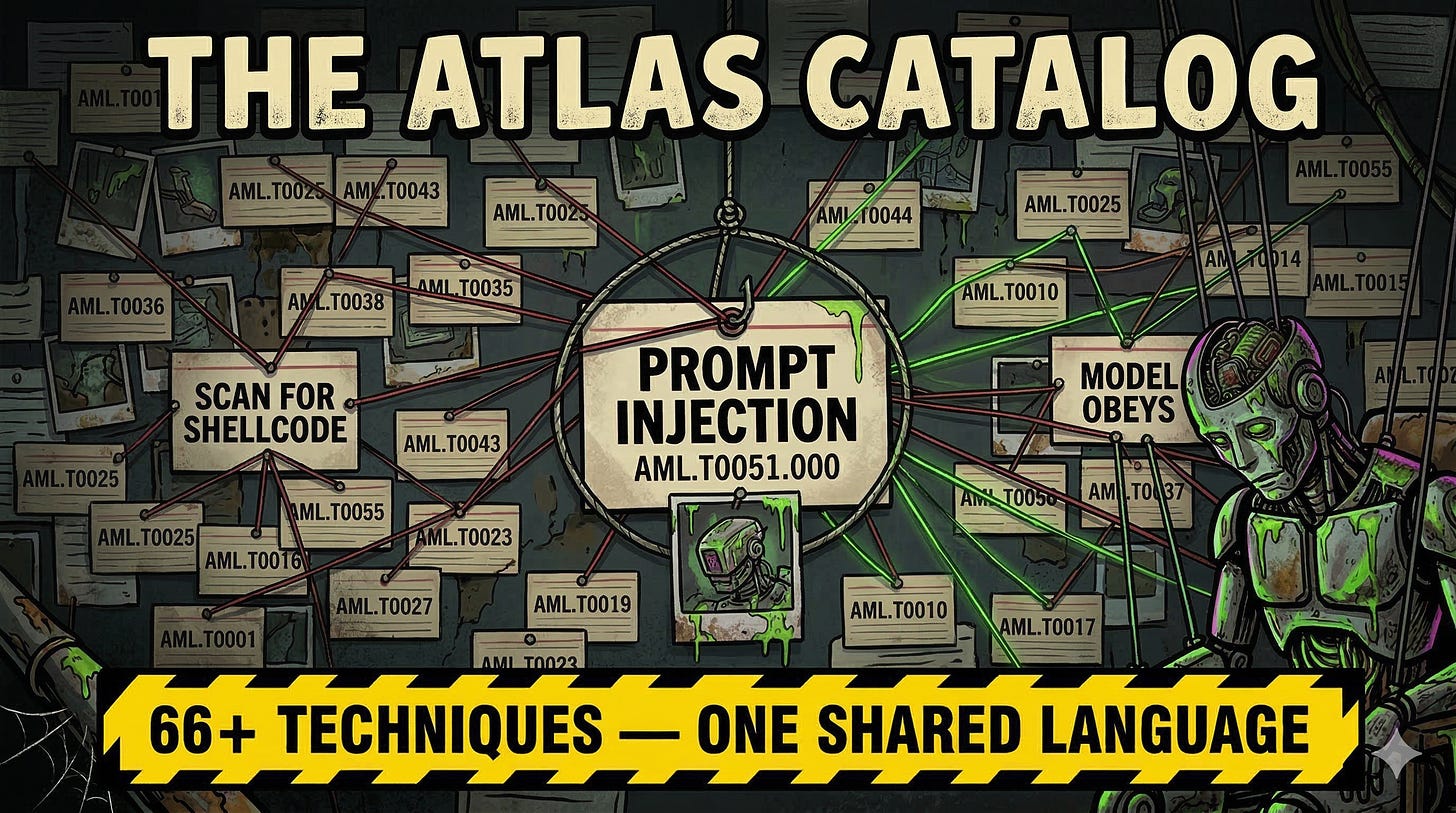
ATLAS (Adversarial Threat Landscape for AI Systems) is a matrix of 14 attack tactics and 66+ techniques, organized from Reconnaissance through Impact. If you’ve used MITRE ATT&CK for traditional security (the framework that assigns technique IDs like T1566 for phishing), ATLAS is the same idea applied to AI. Every attack technique gets a unique ID, a description, and real case studies.
Why this matters: when your red team finds a prompt injection that bypasses guardrails, ATLAS gives you a standard way to document it. Write AML.T0051.000 on the ticket instead of “the chatbot did something weird.” Your SOC, your compliance team, and your vendor all speak the same language.
In February 2026, MITRE published an investigation into attacks against the OpenClaw AI agent. They mapped real exploit chains to ATLAS technique IDs, including a one-click RCE that chained a browser-based CSRF attack into a full sandbox escape. That’s the value: not theory, but documented attacks with technique IDs your tooling can reference.
NVIDIA tells you the attack has five chapters. ATLAS tells you what happens in each sentence. Use both.
Wondering how deep the rabbit hole goes?
Paid is where we stop pulling punches. Raw intel nuked by advertisers, complete archive, private Q&As, and early drops.
Frequently Asked Questions
What Is the AI Kill Chain?
The AI kill chain maps the stages of an attack against an AI system, from initial reconnaissance through final impact. Unlike the traditional Cyber Kill Chain built for network intrusions, the AI version focuses on how attackers manipulate model behavior through poisoned inputs, hijacked inference, and abused tool permissions. The concept: break any link and the attack fails.
What Is the Difference Between NVIDIA’s AI Kill Chain and MITRE ATLAS?
NVIDIA’s AI Kill Chain is a five-stage narrative model that shows how an attack progresses against an AI application. MITRE ATLAS is a technique catalog with 14 tactics and 66+ techniques that gives each attack behavior a unique ID. NVIDIA tells you the story. ATLAS gives you the index. Most security teams use both together.
Can Traditional Security Tools Detect AI Kill Chain Attacks?
Partially. Endpoint detection catches known malware, and web application firewalls catch known injection patterns. But an AI agent chaining legitimate tool calls into a destructive outcome, using valid credentials within normal rate limits, slips past both. The detection gap is at the AI session level, where sequences of normal-looking actions add up to compromise.





Feel free to AMA! If your new to AI security, the kill chain is a great place to start learning.
Okay, what can I do? Help me