TL;DR: The IBM X-Force 2026 Threat Intelligence Index tracked a 44% spike in public-facing app exploitation, over 300,000 stolen ChatGPT credentials on dark web markets, 109 active ransomware groups, and a 4x increase in supply chain compromises since 2020. Vulnerability exploitation is now the #1 initial access vector, and AI made every step faster.
This is the public feed.
Upgrade to see what doesn’t make it out.
0x00: How AI Vulnerability Discovery Changed the IBM X-Force 2026 Numbers
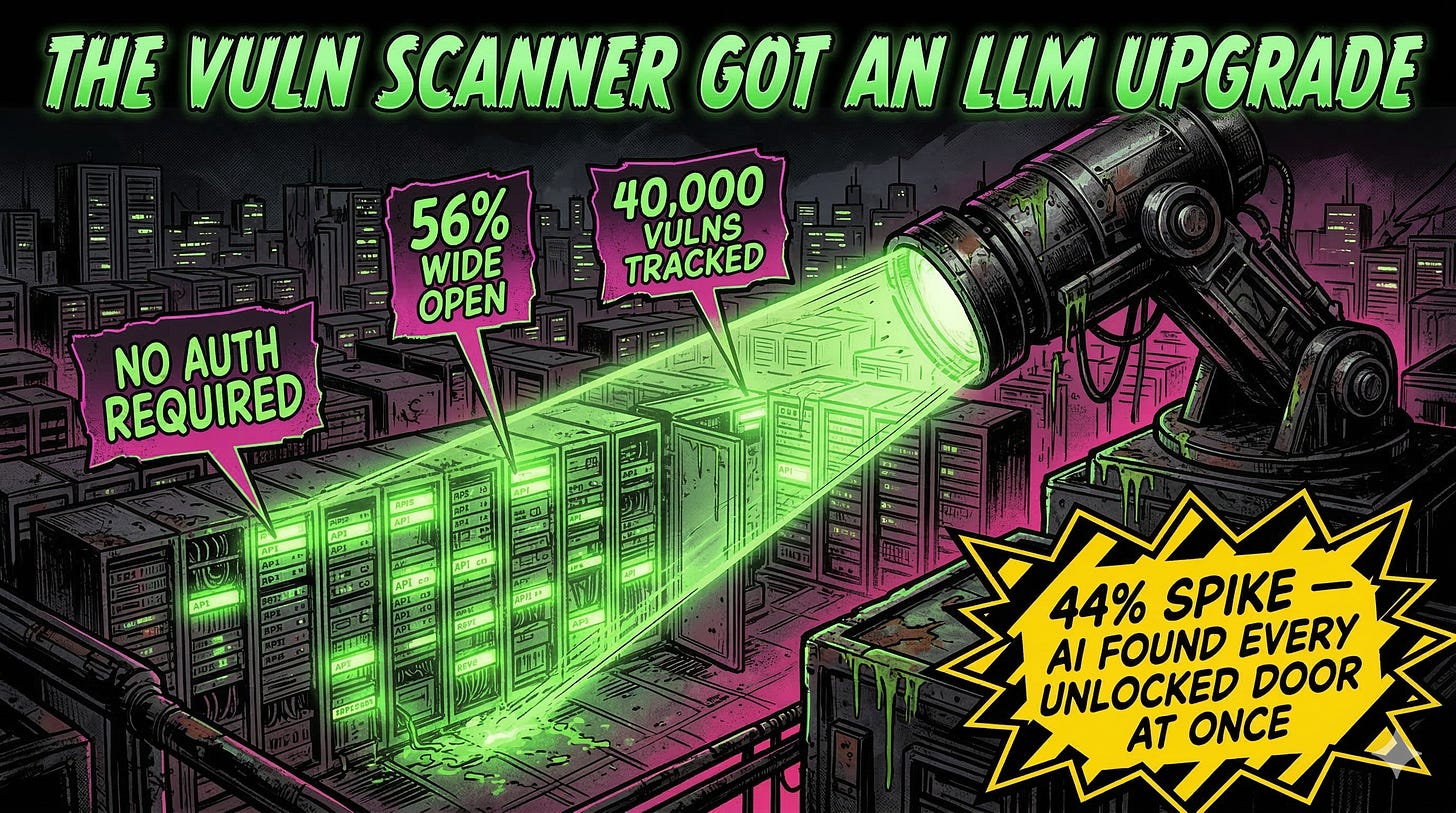
IBM X-Force tracked a 44% year-over-year increase in attacks beginning with exploitation of public-facing applications. The 2026 X-Force Threat Intelligence Index pins the cause on two things: missing authentication controls and AI-enabled vulnerability discovery. We’ve moved past script kiddies lobbing Nmap scans at random /16 blocks. Models now parse exposed API docs, fingerprint stacks, and correlate unpatched versions against known exploit chains faster than a SOC analyst can finish morning standup.
Here’s the number that should keep you up: 56% of the vulns X-Force tracked in 2025 required zero authentication to exploit. No credential bypass needed because there was no credential requirement in the first place. Wide-open endpoints, sitting on the internet, and AI made it trivially easy to find every single one at scale. X-Force tracked nearly 40,000 vulnerabilities across the year. The combination of misconfigured access controls and increasingly complex application stacks gave attackers a buffet of exposed surfaces, and the models brought the appetite.
Signal boost this before someone else gets owned.
0x01: Why 300,000 Stolen ChatGPT Credentials Landed on the Dark Web
Infostealers expanded their target lists in 2025. X-Force found over 300,000 ChatGPT credential sets advertised on dark web markets, harvested by commodity malware like Raccoon and Vidar. The same families that grab browser cookies and SSO tokens now grab AI session credentials too. IBM flagged this as a signal: AI platforms now carry the same credential risk as core enterprise SaaS.
A compromised chatbot login opens a different kind of exposure. Inside someone’s ChatGPT account, an attacker reads every conversation the user had with the model. Proprietary code reviews, strategy documents pasted in for summarization, internal data used as context. Then there’s the offensive angle: prompt injection from the attacker side, manipulating outputs, poisoning future sessions, exfiltrating data the user feeds in next. Password reuse between personal and enterprise accounts creates lateral paths that credential stuffing tools eat for breakfast. If your org hasn’t scoped AI platforms into its credential monitoring program, this is the wake-up call. The voluntary exfiltration problem we wrote about last year just got a receipt from IBM’s incident data.
How many of your users are reusing their ChatGPT password on corp SSO right now?
0x02: How Ransomware Ecosystem Fragmentation Accelerates AI-Driven Attacks
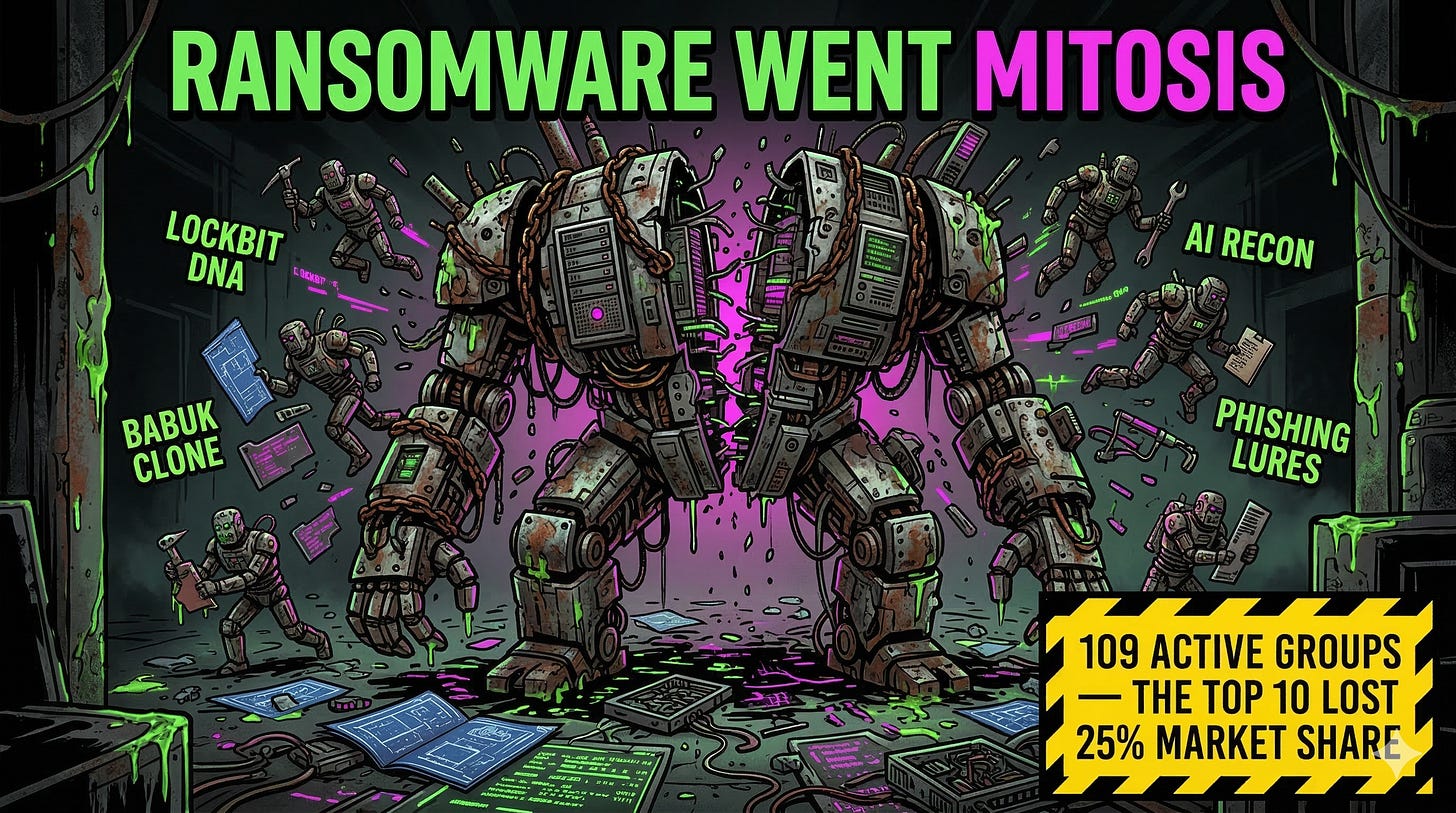
The big gangs fractured. X-Force counted 109 distinct ransomware and extortion groups in 2025, up from 73 the year before. That’s a 49% jump. The top 10 groups’ share of total activity dropped 25%, meaning the long tail got longer and noisier. Smaller cells, harder to attribute, harder to predict.
Leaked tooling lit the fuse. Builder kits from LockBit and Babuk made it trivial for any halfway competent crew to stand up a ransomware operation overnight. Stack AI on top and these small shops automate recon, craft phishing lures, and adapt payloads without a dedicated dev team. The IBM newsroom release puts it bluntly: attackers reuse playbooks and tap AI to automate operations. Manufacturing stayed the most targeted sector at 27.7% of incidents. Financial services sat right behind it. North America ate 29% of all observed attacks, the most-targeted region for the first time in six years.
0x03: Why Supply Chain Attacks Quadrupled Since 2020
Supply chain compromises nearly quadrupled over five years. Attackers target CI/CD pipelines, poison trusted developer identities, and ride SaaS integration trust relationships downstream into production environments. Rather than breaking through the front door, they walk in through a vendor’s back door with valid creds. Nick Bradley from X-Force Threat Intelligence nailed the mechanic: modern software sits on sprawling webs of dependencies, cloud services, and APIs, and the connectivity itself creates the vulnerability.
AI coding assistants accelerate this problem. More code gets shipped faster, and that code occasionally pulls in unvetted dependencies that nobody audits until the breach report drops. Vulnerability exploitation hit 40% of all incidents X-Force responded to in 2025, making it the single most common initial access vector. The blurring line between nation-state and financially motivated operators means the talent pool doing this work is deep and getting deeper. Techniques that used to live in APT playbooks are showing up in financially motivated campaigns because the AI kill chain doesn’t care who’s pulling the trigger. You can run a perfect security program internally, patch everything, train your users, enforce MFA. Then a third-party vendor gets popped through their build pipeline and your data shows up in the breach report anyway.
Wondering how deep the rabbit hole goes?
Paid is where we stop pulling punches. Complete archive, private Q&As, and early drops.
Frequently Asked Questions
What are the biggest findings in the IBM X-Force 2026 Threat Intelligence Index?
The report tracked a 44% increase in public-facing application exploitation, over 300,000 stolen ChatGPT credentials on dark web markets, 109 active ransomware and extortion groups (up 49%), and a nearly 4x increase in supply chain compromises since 2020. Vulnerability exploitation became the leading cause of all incidents at 40%, and 56% of exploited vulnerabilities required no authentication.
How is AI changing cyberattack tactics in 2026?
AI accelerates the attacker lifecycle at every stage. Models automate vulnerability discovery, fingerprint exposed stacks, and correlate unpatched versions against known exploits at scale. Ransomware crews use AI for recon, phishing lure generation, and payload adaptation. AI coding tools also introduce supply chain risk by shipping unvetted dependencies faster than security teams can audit them.
Which industries were most targeted according to IBM X-Force 2026?
Manufacturing topped the list at 27.7% of all incidents observed by X-Force, followed by financial services and insurance. North America became the most-targeted region for the first time in six years, absorbing 29% of total attacks, up from 24% in 2024.