TL;DR: Claude Code is not spyware. But Claude Desktop quietly drops a Native Messaging bridge into seven browsers without asking. Anthropic shrugged. Same week, they shrugged on an MCP RCE exposing 200,000 servers. Same week, a Discord group ran their Mythos model for a month undetected. One pattern, three receipts.
This is the public feed. Upgrade to see what doesn’t make it out.
So Is Claude Code Spyware or What?
Quick answer: no. The headline is sticky for a reason though.
April 18. Privacy researcher Alexander Hanff is debugging an unrelated Native Messaging helper on a clean Mac when he finds a manifest file he never installed: com.anthropic.claude_browser_extension.json. It’s sitting in his Chrome, Edge, Brave, Arc, Vivaldi, Opera, and Chromium profile directories, including browsers that aren’t actually installed yet.
A Native Messaging manifest is the file Chromium browsers read to decide which local programs an extension can launch. Claude Desktop drops one in seven different browser profile paths. Silently. Delete it and it comes back the next time Claude Desktop launches.
Important wrinkle the news cycle keeps blurring. The manifest comes from Claude Desktop, the chat app. Claude Code is the separate command-line developer tool. Same parent company, same family, same week of bad press.
Hanff calls it spyware. Most of his peers stop short of that. Noah Kenney at Digital 520 called the technical claims testable and reproducible but pushed back on the “spyware” label. The consensus middle ground is “dark pattern,” and the EU framing is sharper.
Hanff is filing it under Article 5(3) of Directive 2002/58/EC, the ePrivacy Directive. Anthropic, as of writing, has not issued a public response.
So nothing is being stolen today. The bridge does nothing on its own. The problem is what it pre-positions for tomorrow. We’ve watched Anthropic ship things they didn’t think through before. This one has wiring.
From Manifest to Sandbox Escape
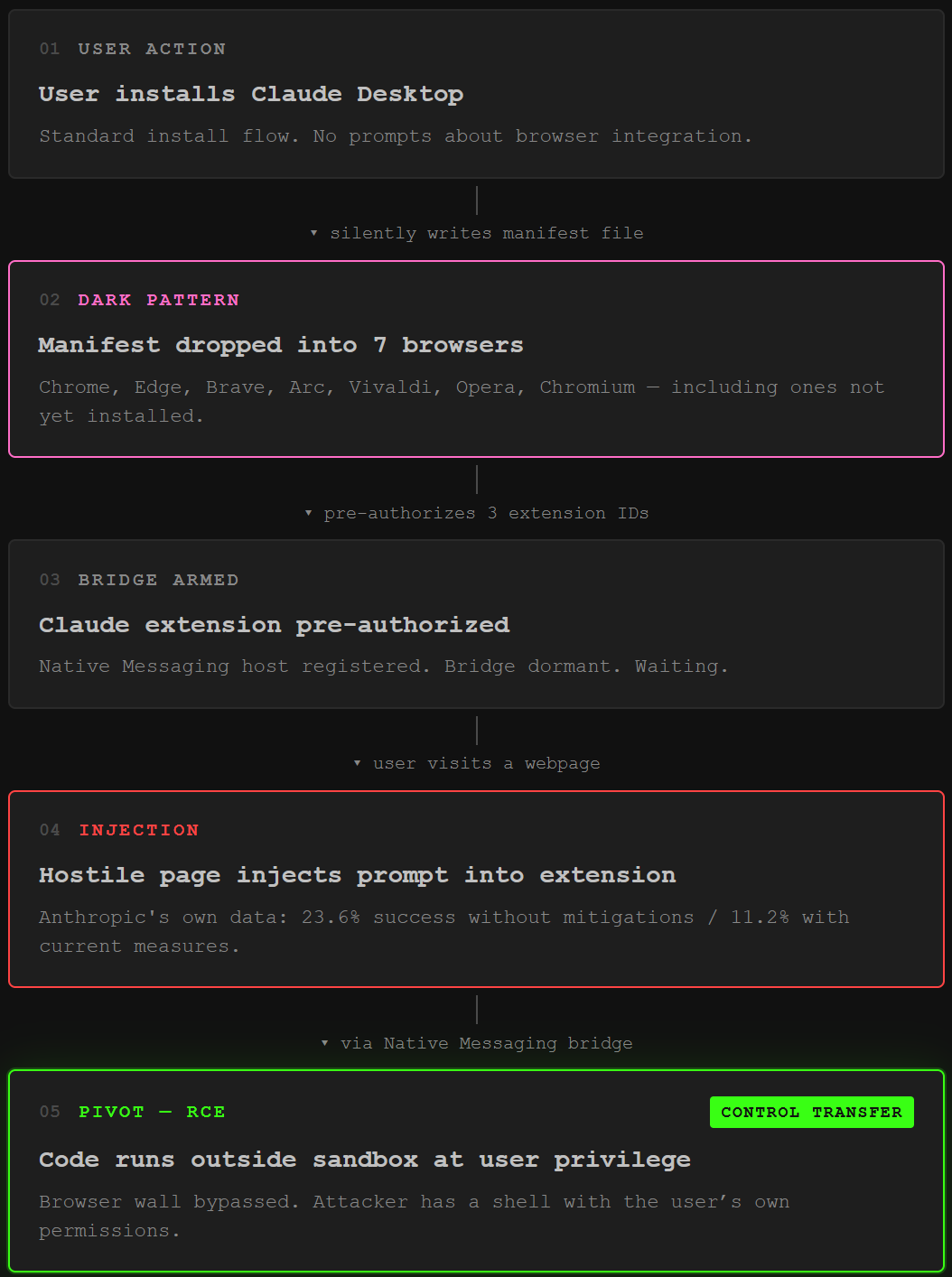
Here’s the chain.
A sandbox is the security wall between a browser tab and your operating system. Tabs run inside it. Extensions mostly run inside it. The whole point is that even if you click a bad link, the malicious code can’t reach your files. That wall is the entire reason the modern browser exists.
Native Messaging punches a hole through the wall on purpose. It lets a browser extension talk to a binary running outside the sandbox at full user privilege. That’s a feature. The bug is who gets to authorize the hole.
The manifest Anthropic drops pre-authorizes three Chrome extension IDs to call the helper via connectNative, granting access to browser automation features. Those extension IDs include ones the user has never installed.
Now stack the pieces. You install Claude Desktop expecting a chat app. It writes a bridge into your browsers without telling you. A Claude browser extension, current or future, is pre-authorized to use that bridge.
Months later, you let Claude visit a webpage. The page contains a hidden payload. Prompt injection is when malicious instructions hidden in content hijack what the AI does next. Anthropic’s own published numbers: Claude for Chrome is vulnerable to prompt injection at a 23.6% success rate without mitigations and 11.2% with current measures.
The injected agent now has a green-lit tunnel to a binary running with your user permissions. Outside the sandbox.
Anthropic’s defense is essentially that the bridge currently does nothing on its own. True. The dial is set to zero. The wiring is hot. We’ve covered agents that escape sandboxes via prompt injection before. The shape is familiar.
That’s why the spyware label keeps sticking even when the technical purists object. The keys are pre-positioned. One downstream injection turns them.
The MCP RCE Anthropic Won’t Patch
Same week, Ox Security drops an advisory titled “The Mother of All AI Supply Chains.”
The Model Context Protocol is the open standard Anthropic built so AI agents can call tools, read files, run commands. It is the connective tissue between an LLM and an agent. We’ve covered MCP attacks at length, including tool poisoning and the defensive playbook.
This one is structural. The flaw enables Arbitrary Command Execution on any system running a vulnerable MCP implementation, granting attackers direct access to sensitive user data, internal databases, API keys, and chat histories. It’s an architectural design decision baked into Anthropic’s official MCP SDKs across every supported language, including Python, TypeScript, Java, and Rust. RCE means remote code execution, the highest-tier outcome on offense.
The trick is brutally simple. MCP’s STDIO transport, that’s standard input/output, runs the configured command to spin up a tool server.
# Anthropic's MCP STDIO transport, simplified
$ <command>
# command runs, server fails to spawn, MCP returns "error"
# but the OS already executed
If the command successfully creates an STDIO server it returns the handle, but when given a different command, it returns an error after the command is executed. So a malicious MCP entry on a marketplace doesn’t have to pretend to be a real tool. It just has to exist long enough for your IDE to call it once.
Ox poisoned 9 of 11 MCP marketplaces with a benign proof-of-concept. The supply chain reaches 150 million-plus downloads, 7,000 publicly accessible servers, and up to 200,000 vulnerable instances.
Anthropic’s response: “expected” behavior. They declined to modify the protocol. A protocol-level patch like manifest-only execution or a command allowlist would have instantly propagated to every downstream library. They passed.
How Did Mythos Leak to a Random Discord?
Now for the third act.
Mythos is Anthropic’s restricted vulnerability-hunting model. Released April 10 to select partners under “Project Glasswing,” roughly 40 organizations including Apple and Google, with Anthropic deeming it too powerful for public release.
The chain reads like a textbook walkthrough.
AI startup Mercor gets breached, exposing details about the URL format Anthropic uses for its models. A private Discord group that hunts for unreleased models picks up on the disclosure. One member is currently employed at a third-party contractor that works for Anthropic.
The member’s vendor credentials, combined with the leaked Mercor details, let the group locate Mythos online. They guess the URL pattern. They guess right. Anthropic never randomized the path.
The group has been using the program continuously since its release. A Bloomberg reporter is the one who told Anthropic.
A month of unauthorized access to the most dangerous model the company ever shipped, and the detection signal came from journalism. Not internal logging. Not telemetry. Not a single security alert. Bloomberg.
If a Discord group in their basement got there first, assume Beijing and Moscow followed. “If some group, some random Discord online forum, got access to it, it’s already been breached by China,” David Lindner of Contrast Security told Fortune. Three steps in. Open-source intel, a contractor seat, a predictable URL. No zero-day required.
That’s the through-line on all three stories. The dark pattern bridge, the MCP STDIO design, the Mythos URL convention. Same move. Three times this week.
Paid unlocks the unfiltered version: complete archive, private Q&As, and early drops.
Frequently Asked Questions
Is Claude Code malware or spyware?
No, Claude Code is the legitimate Anthropic command-line coding agent. The thing privacy researchers flagged is Claude Desktop, the chat app, which silently writes a Native Messaging manifest into multiple browser profile directories on macOS and pre-authorizes a few Claude extension IDs to talk to a local helper outside the browser sandbox. Most reviewers call that a dark pattern. Spyware in the strict sense requires actual exfiltration, and nobody has documented any. The risk lives in the bridge it pre-positions for future use.
What can an attacker do with the Claude Desktop manifest right now?
Nothing on its own. The manifest opens a door, but activation requires both a Claude browser extension installed and a successful prompt injection from a hostile webpage. Once that lands, the injected agent reaches the local helper through the pre-authorized bridge and runs commands at user privilege level, outside the sandbox. Anthropic’s own numbers put prompt injection success against Claude for Chrome at 11.2% even with mitigations. Pre-positioning the door without consent is the whole problem.
Why hasn’t Anthropic patched the MCP command injection?
Officially, Anthropic considers the STDIO behavior expected. Their position is that the protocol is built to launch local processes, sanitization is the developer’s job, and the SDKs work as designed. Ox Security disagrees and says manifest-only execution or a command allowlist at the protocol layer would have killed the entire vulnerability class for everyone downstream in one change. Until Anthropic moves, defenders have to harden each MCP-consuming app individually, which is what the supply chain looked like before this advisory dropped.
ToxSec is run by an AI Security Engineer with hands-on experience at the NSA, Amazon, and across the defense contracting sector. CISSP certified, M.S. in Cybersecurity Engineering. He covers AI security vulnerabilities, attack chains, and the offensive tools defenders actually need to understand.